The term Antivirus refers to the common means of fighting computer malware. While hackers have become very much skilled and prolific in their spread of malware, conventional antivirus is being augmented with more advanced techniques and features. Antivirus software has become one component of security suites that offer multi-layered protection for computers. Our partner ESET is an example of an antivirus software company.
Today, it is simply impossible to have a functional and safe computer system without adequate antivirus protection.
As Rep. Will Hurd said in his opening statement to the Subcommittee on Information Technology, Federal CyberSecurity Detection, Response, & Mitigation hearing that took place in April 2016, “Attacks on both the public and private sectors consistently reveal one common truth – no one is immune“.
Key benefits of antivirus solutions for your small business:
1. Keeping your system safe from trojans, spyware, computer viruses and worms, password and data theft, and other malware threats
Trojans
A Trojan is a common reference to a malicious computer program that is used to hack into a system by using deception strategies to trick users to deploy the program – like a Trojan Horse full of Greek soldiers were used to trick citizens of Troy.
Trojans are non-replicating, and are generally spread by some form of social engineering: they appear to be benign, yet they are malicious. Some Trojans may be hard to detect, since by nature they are designed to deceive the user by appearing to be a legitimate source or program, and typically do not interrupt the user experience. Trojans often use obfuscation techniques.
A typical scenario would involve a user being misled into clicking on the link or opening an e-mail attachment of an email disguised to be from a trusted source – an official organization, a friend, or someone who needs help. Although their goals can vary, many forms act as a backdoor, providing unauthorized access to the infected computer system. Trojans typically do not infect other files nor do they propagate.
Viruses
Computer viruses typically reproduce themselves and then modify other programs on the infected machine. They can also affect CPU time, hard disk space. To make it worse, they can corrupt your data force unacceptable content on the screen, access and steal private information. Your computer may get corrupted to the point where it can no longer be used.
Viruses rely on being executed either by the system’s operating system (compiled viruses) or an application (interpreted viruses). Most viruses employ obfuscation methods – ways of creating a virus that make it very difficult to detect, increasing its chances to spread further. Without an antivirus, it is probably impossible to clean out infected systems.
Worms
Unlike viruses, worms are self-contained and do not require a host application, and generally are not as destructive as viruses. They usually replicate themselves by creating functional copies of themselves and continue spreading to other systems in a computer network: they can propagate exponentially. Typically worm infection results in unhealthy bandwidth that halts network traffic. While generally they are not designed to corrupt the data, some worms may delete files. There are several types of worms, such as network service worms, and mass-mailing worms.
Spies
Some malware is spies – a good example would be an AutoCAD Bourne: its primary purpose is not to be destructive, but to perform industrial espionage, by sending copies of proprietary DWG files to a file-sharing server in China for a period of time.
“The infamous deficient cybersecurity at Hillary Clinton’s State Department could have negative implications for American businesses, a House panel heard on Wednesday, due to vulnerabilities that foreign actors have been able to exploit in the quest to steal trade secrets”. (Washington Examiner: “Deficient State Department cybersecurity threatens small business“)
Keystroke Loggers
Spy cousins, keystroke loggers monitor, and record users’ keyboard activities. The main goal of an average keylogger is to gain information details on user passwords and usernames to local or remote systems, and external web sources, emails, personal, sensitive, and financial data.
Keyloggers can use multiple resources to steal your credentials. Take KeyBase as an example: while it was active (it is currently shut down), it was able to extract sensitive data such as passwords from sources such as Facebook, Google, Youtube…
Take a quick look at this list of applications:
- Browsers:
- Google Chrome
- Mozilla Firefox
- Internet Explorer
- Opera
- Safari
- Mail Clients
- Microsoft Outlook
- Thunderbird
- Incredimail
- Netscape
- Eudora
- Other apps:
- FileZilla
- JDownloader
- IDM
- IMVU
- PalTalk
A keylogger can also retrieve clipboard text (what you use in copy/paste), and do other types of malice.
If a keylogger like KeyBase makes it to your system, what type of information do you think will be compromised? Without a good antivirus, your system is vulnerable to cybercriminals.
Adware
Adware is a form of malicious software that downloads and keeps displaying an unsolicited advertisement when you are using an internet browser, without your authorization. It may also redirect search queries to advertising websites. The ads generated by adware often come in the form of pop-ups that are often impossible to close or to get rid of.
Malware in general
“Malware, short for malicious software, is a blanket term for any software used to disrupt computer operations, gather sensitive information, gain access to private computer systems, or display unwanted advertising.” (Wikipedia)
Antivirus software is used to remove or prevent malware from getting into your computer, protect a computer system from malware such as viruses, computer worms, Trojans, spyware, adware, and other forms of malicious software.
2. Maximizing your defense against new and unknown threats by stopping most threats proactively
Antivirus software relies on signatures to identify malware – a unique binary pattern, a fingerprint of a virus. Anti-virus software uses the virus signature to compare code and scan for the sign of malicious code. When an antivirus firm analyzes a new suspect and determines it to be malware and a signature is detected, it is added to the database of the antivirus software. With proper antivirus installed, small signature updates take place as needed, and discretely not to interrupt your system’s performance.
That is why it is so important to always keep your antivirus up-to-date.
3. Enabling users to share files with confidence by stopping threats from accessing your system via removable devices.
 Several additional levels of scanning on removable media are typically offered by vendors. A “removable device” is a device or equipment that can be temporarily connected to the computer. It may be a memory card, a USB stick, memory card, flash drive, external hard drive, camera, etc.
Several additional levels of scanning on removable media are typically offered by vendors. A “removable device” is a device or equipment that can be temporarily connected to the computer. It may be a memory card, a USB stick, memory card, flash drive, external hard drive, camera, etc.
Due to their portability, external devices are an attractive and convenient medium for spreading computer viruses. Portable and removable devices are vulnerable to two major types of viruses: the shortcut virus and the autorun virus.
For self-running media, the antivirus can perform on-access and on-demand scans: when the removable media is inserted, files can be scanned when the removable device is first accessed, or perform a full scan of the media on demand.
4. Scan and clean email and Internet traffic, including SSL-encrypted content, so your emails are always safe.
Email antivirus is a component in charge of scanning suspicious objects in both incoming and outgoing emails, search for danger.
Email antivirus starts on a system startup and resides in computer memory. By default, the component intercepts each email and splits it into three parts: header, body, and attachment. It then uses the antivirus databases and heuristic analyzer to scan the body and the attachment for dangerous objects.
Encrypted traffic can contain malicious files, or an end-user may be sending confidential information via an encrypted channel. Historically the problem was that due to its nature SSL-encrypted content could not be scanned on arrival or departure. Modern well-known anti-virus software such as ESET, Kaspersky, and Bitdefender now offer options for scanning encrypted email content.
5. Protection from Spam
Spam is annoying. Nobody likes spam. It would be safe to say that everyone hates spam (expect spam-makers, maybe…) that bombards your mailbox with junk and ads you never requested.
To top that, nobody decent wants to be spamming others – but it can happen unbeknownst to the user. In addition to usual spamming sources, spam can be sent and received as a result of a virus that discretely takes over a computer system. Since antivirus protection software can keep your computer system clean from viruses, having a good antivirus installed and properly maintained should drastically reduce spam.
There are many types of anti-virus protection applications to choose from, and the best products offer nearly complete shielding from viruses, spyware, and spam.
6. Performance metrics, system diagnostics, and recovery
The reputable software offers reports that show the performance of the antivirus, anti-spyware, and real-time protection modules, in form of easy-to-understand graphs and statistics.
When the diagnosis is performed you get access to a report that includes system information and configuration details and includes the status and data on system response times, local hardware resources. and processes on your system. If your computer’s performance is falling behind or another issue is detected, a system diagnostics report containing information about problems and suggestions of how to fix them allows your technicians to streamline systems operation and maximize performance.
7. Real-time an on-demand protection
Having an antivirus program on the computer system allows you to actively scan resources as they enter your system – before they get in and activate. Think of it as a scanner that serves as a shield defending your computer and your network by either removing or placing suspicious files into quarantine. Antivirus can also run a boot-time scan.
Antivirus also provides the ability to scan individual files and programs before any user interaction.
Protecting private and sensitive information
Antivirus defends against malware that is capable of using systems to broadcast itself to other systems and make your computer into a platform for more malware. Not only you can unknowingly forward malware to anyone in your contact lists if your computer is infected, but you can also have your most sensitive and private information forwarded to illegal botnets (networks of compromised computers that specializes in the theft of valuable data destined to be sent to criminals and sold to interested third parties). The “Ramnit” is an example of such a botnet virus. During 5 years in 2011-2015, it affected 3.2 million Windows systems before Ramnit’s takedown by Europol in January of 2015.
Most often viruses, worms, trojans, spies, and other forms of malware rely on security failure when they target your computer. Minimize the threat by keeping operating systems and software up-to-date, run firewall and antivirus software, and be smart about opening unrecognized or unexpected emails and their attachments and links.
Anti-virus and Anti-malware Solutions for Small Business
Choosing an antivirus may not be as easy as it seems because they are not all created equal. They differ in features, performance tests, and price. There is an overwhelming number of options out there; how to decide which antivirus program is best for your business?
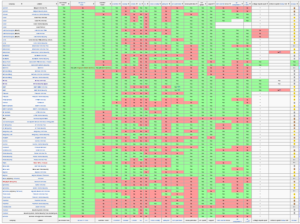
Here is a representative screenshot of the antivirus features comparison just for Windows desktops and servers represented at Wikipedia. It gives you an idea of how much can go into a decision-making process when choosing an antivirus software that fits specific business needs.
To make things more complex, various sources publish their own “top 10” reviews, and sometimes they differ from source to source. In addition, one good antivirus program that performed great yesterday can have a major vulnerability today, as it happens with Symantec (CNN: “Symantec – the popular computer protector – may actually help hackers, feds warn“)
SMBs often have different needs than individuals or large corporations, and it applies to antivirus software, as well. The size of the organization and its respective computer network of each SMB are different, and their business-specific, mission-critical applications further affect variables and diverse setups, from organization to organization. Antivirus solutions for one small business may be different from another, ranging from standard to advance.
Managed Antivirus Solutions
Just getting antivirus software installed is not enough. Left unmanaged, it can still leave the computer network vulnerable, because it depends on the end-user to run or to deny updates install patches, and possibly disable the program. If you choose Unmanaged Antivirus for your business, you will need to exercise discipline and responsibility. Make you keep your licensed antivirus up-to-date, not just when you have time, but on a regular basis. Also, remember to train your employees on matters of security, and enforce policies and procedures regularly.
To choose the antivirus that would work best for your organization we recommend consulting with a trusted, professional IT solutions and Managed Services company, with a proven record of providing antivirus solutions and technical support for their clients. If dealing with an unmanaged antivirus is too much for your organization, consider hiring a Managed Services Provider.
A Managed Antivirus Solution is typically provided by antivirus software expert IT partners who take care of installing and proactively managing the software on computers, servers, and other devices going forward. When you engage with a Managed Services Provider, it becomes their job and responsibility to ensure that the antivirus and definitions are up-to-date, that regularly scheduled scans are set for a time convenient to end-users, without interrupting their work processes, protecting computer network.
Need to hire a Managed Services Provider for your business IT needs?
As an award-winning Managed IT Services and Tech support provider we offer computer and network services including Managed IT Services, Technical Support, and Small Business computer consulting in New Jersey, NY Metro, and surrounding areas.
With our complete, IT support monthly plans for your business you can have a predictable budget for your IT needs and peace of mind knowing your systems are at their top performance level. We provide tech support services and antivirus solutions for proactive defense, fast, effective, and straightforward protection for your computer network. Top-of-the-line software protects your computer use experience without getting in your way.
Get dependable, reliable computer services and IT support for your small business: call (201) 4931414.
How is your state of IT? Call Us: (201) 493-1414 with any questions.