The New Jersey Cybersecurity & Communications Integration Cell (NJCCIC), in which powersolution is a member of, issued an alert around a new email threat. Cyber criminals are using fake business productivity suite emails to harvest credentials. Emails are mimicking SharePoint Online, One Drive, Drop Box share notifications as well as an awaiting message in Teams or SLACK.
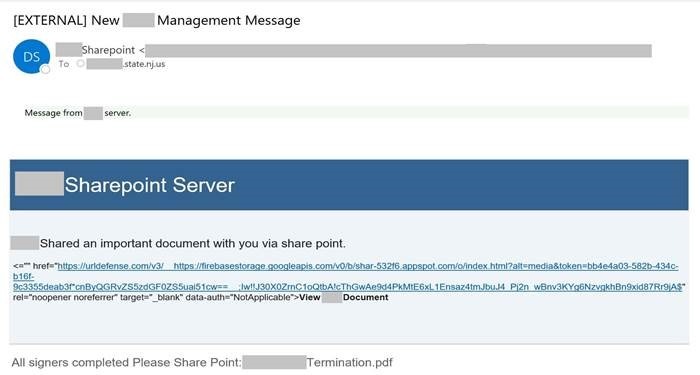
A sample of a fake email is below:
The way organizations conduct business and how users access corporate networks, resources, and data have changed significantly with the dramatic increase in remote workforce this year, resulting in vulnerable people, processes, and technology. Organizations depend on secure and reputable business productivity suites, such as Microsoft 365, to work more effectively, particularly when in a remote environment. The widespread use and dependence on these services, however, makes them desirable targets of malicious cyber activity. During the first half of 2020, researchers discovered a 176 percent increase in new malware attacks disguised as trusted Microsoft Office file types.
Cyber-criminals continue to target Microsoft 365 users with convincing phishing campaigns, oftentimes in an attempt to steal login credentials.
The emails are purportedly sent from within the target’s organization, a claim reinforced by the sender’s display name and the repetitive inclusions of the target’s organization, and appear to be automated Microsoft SharePoint notifications that invite the recipient to open or view documents. The emails are brief, vague, and contain a link that, if clicked, directs the target through multiple redirects to a spoofed Microsoft SharePoint authentication webpage. If credentials are entered, they are sent to the cyber-criminals in the background, providing them with the opportunity, to gain unauthorized access that allows them to launch internal attacks, steal additional credentials or data from the organization, and more. Other observed Microsoft SharePoint phishing campaigns inviting recipients to open or view files include themes of orders, payment confirmations, electronic funds transfer (EFT) enrollments, and voicemail messages.
Recommendations
- Implement a defense-in-depth cybersecurity strategy and educate yourselves and others on these continuing threats and tactics to reduce victimization.
- Users are advised to exercise caution with links, attachments, and spoofed domains received from both unknown and trusted senders.
- Navigate directly to authentic vendor websites
- Keep applications up to date.
- If you are unsure of an email’s legitimacy, contact the sender via a separate means of communication.
Additionally, powersolution.com’s guidance is to ensure both on-corporate network devices and off-corporate devices have the proper security solutions in place, such as Antivirus/Antimalware, DNS based filtering, hardware/software firewalls, and email security. Although no technology based solution will stop 100% of the threats, by combining many different solutions that interact with data on different streams, the chance of a cyber-threat is reduced. Ultimately, as the NJCCIC states, it is up to the end user to be the last line of defense.
If you would like to discuss cybersecurity solutions that can better protect your office from this new threat and other cyber threats, please contact powersolution.com at (201) 4931414.
How is your state of IT? Call Us: (201) 493-1414 with any questions.

