Tax season is here and attackers have been aggressively targeting popular tax software to harvest credentials. The software provider Intuit has issued a few security notices of a significant increase in fake emails pretending to be sent by Intuit’s notification system.
Intuit has now joined the ranks of household names such as American Express, Amazon, and other big brand companies whose customers were targeted in phishing campaigns. You may be among those who recently received a fake email like the one below.
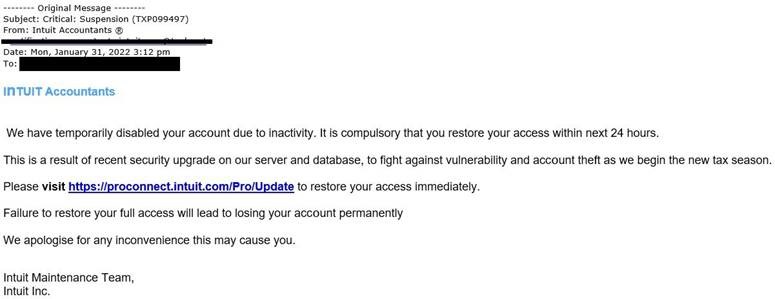
The “Intuit” version of the malicious email implies that your account has been suspended and invites you to click on the link to restore access. By clicking the link in the email, you will be taken to a fake landing page asking to enter your account credentials. By doing so, you will be unknowingly providing your login credentials to the attackers.
Intuit’s alert follows reports received from customers who were emailed and told that their Intuit accounts were disabled following a recent server security upgrade.
The verbiage in the fake email includes “We have temporarily disabled your account due to inactivity. It is compulsory that you restore your access within next 24 hours,” as well as “This is a result of recent security upgrade on our server and database, to fight against vulnerability and account theft as we begin the new tax season.“
Intuit said that it’s not behind these emails and that the sender “is not associated with Intuit, is not an authorized agent of Intuit, nor is their use of Intuit’s brands authorized by Intuit.”
powersolution.com recommends users and organizations educate themselves and others on these continuing threats and tactics to reduce victimization. We remind users to exercise caution with unsolicited emails. Additionally, be aware of unusual requests when contacting a customer service call center – legitimate businesses do not typically request users to download Excel documents or disable antivirus. If a request is suspicious, do not comply with the request, cease communication, and use your email and network security protocols.
Email Security Tips:
- Verify the source and instructions of any monetary transaction or other unusual requests received via email through a separate means of communication, such as a phone call. Replies to the email could be sent to the threat actor and is not an effective verification method.
- Hover over the email sender name to determine if the address used to send the email is different than who the user claims to be.
- Look for red flags in emails including, but not limited to:
- The email contains poor spelling or grammar.
- The request conveys a sense of urgency.
- The appearance – as if it was sent via a mobile device.
- The request reference goods or services you are unfamiliar with.
- The sender identifies themselves in a non-typical way, such as using full names or their first name when they go by their middle name.
- The email is coming from an external source but the sender claims to be someone within your organization.
- Unusual requests, such as a request from the CEO to have all employee W-2’s be sent to them via email or an invoice from a vendor for an abnormally large amount.
How is your state of IT? Call Us: (201) 493-1414 with any questions.

